Overline About Axie Infinity's $625M Ronin Hack and the Dangers of Fake Decentralization
NEW YORK, March 30, 2022 (Newswire.com) - On March 29, Axie Infinity's Ronin Network (Sky Mavis) bridge was exploited for 173,600 Ethereum (ETH) and 25.5M USDC. Approximately one month prior, users of Wormhole — a similar "bridge-based" protocol — fell victim to a 120,000 ETH exploit. Multiple hacks have also targeted validator networks such as Thorchain in recent months. https://www.coindesk.com/tech/2022/03/29/axie-infinitys-ronin-network-suffers-625m-exploit
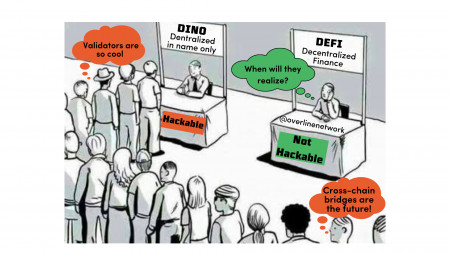
Patrick McConlogue, CEO of the Overline Network, warns: "While the theft of funds itself is appalling, the more glaring issue is the growing acceptance among the crypto community of 'pseudo-decentralization,' a term used to describe centralized services masquerading as decentralized networks in order to evade regulatory scrutiny and capitalize on crypto hype."
Developers of the Overline Network caution that users should be far more skeptical of the claims made by many popular networks today. It is common to see these events labeled as mere exploits and bugs. However, this distances these events from the reality that these attacks are systemic to protocols with bridge, validator or wrapped token designs. These protocols inherently rely on significant concentrations of funds being pooled in contracts developed and controlled by shadowy entities with very little transparency.
While it may seem obvious, the concept of decentralization should involve reducing concentrations of power, not amplifying them. Well-designed networks should be able to function entirely peer-to-peer, where risks of theft are diluted down to the individual level. This is in direct opposition to validator and bridge/pool-based models where validators and contract pools take on the role of quasi-intermediaries.
As Joshua Buirski of the Overline Network put it: "Perhaps the greatest irony is that many have entered the ecosystem lured by the promise of escaping trusted intermediaries, only to unknowingly end up embracing untrusted intermediaries."
For three years, the Overline team has been focused on bringing cross-chain interoperability without the use of validators, intermediaries, bridges, or wrapped tokens to the DeFi space. Adhering to Satoshi's original premise for decentralization, the Overline team took the time to develop a custom proof-of-work consensus model that enables users to trade native coins directly peer-to-peer across different blockchain networks, putting them squarely in control of their own assets and eliminating the risk of contract and validator collusion exploits.
As the industry reflects on the events of the Ronin exploit, it must accept that these events will continue to occur for as long as pseudo-decentralization is tolerated by users. It is important that the industry does not lose sight of the fact that everyone should be building protocols for resiliency, not to compete with the speed and convenience of centralized services. As a community, everyone needs to hold developers to a higher standard and stop tolerating cutting corners where decentralization is concerned.
"The problem with validator-based DEXes on the other hand is that they are not really decentralized and trustless, since we're still trusting a group of validators which supposedly operate at arm's length from each other but are actually incentivized to connect and collude at the expense of unsuspecting users. So while DEXes are more private, the so-called rug-pull risk is much higher there," concludes Buirski.
Overline Network Public Relations: Leila El Hayani | media@overline.network
Source: Overline