Interisle Conducts a Comprehensive Study on the Scope and Distribution of Malware in 2022

NEW YORK, June 20, 2022 (Newswire.com) - In its latest study, Interisle Consulting Group evaluates and provides key insights into the scope and distribution of malware attacks. While studies in recent years have outlined the effects of malware and the consequences of malware infections, Interisle's report instead considers the Internet resources that malware attackers employ and where these malicious programs are hosted.
Having emerged as an organized criminal business, malware has grown to become a global public concern. State actors such as North Korea have been reported to use malware attacks to steal billions of dollars, and Russia deployed destructive malware as part of its incursion into Ukraine. While state-supported and state-sanctioned campaigns have helped generate awareness around malware attacks, both as a law enforcement and a geopolitical issue, this lucrative form of cybercrime remains a rampant problem across a multitude of professional sectors.
Cybercrime, especially malware-related cybercrime, has surpassed fraud as the top predicate offense of concern for corporate compliance teams. Small, midsize, and enterprise-level companies have all suffered extreme financial losses and extended periods of business disruption at the hands of cybercriminals leveraging malicious software such as infostealers and ransomware to execute targeted attacks.
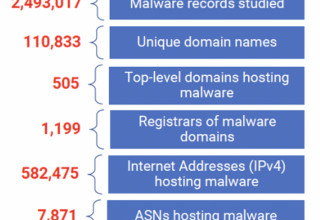
By capturing nearly five million malware reports collected by the Cybercrime Information Center over a 365-day period, Interisle has produced a comprehensive report quantifying how malware perpetrators use Internet resources for nefarious purposes. Interisle's unique malware taxonomy allowed its team to accurately measure and study the most prevalent types of malware, determine where said malware was served from or distributed, and discover which resources criminals were using to carry out their attacks.
The report notes that the most frequently reported malware targets IoT (Internet of Things) devices and that the majority of IoT malware appears to be hosted on networks in the Asia-Pacific region. Per Interisle, networks in the United States and China host the most malware that targets user-attended devices.
"Interisle's report is a comprehensive compilation and presentation on the prevalence of malware. Of particular interest is the focus on a relatively small number of domain registrars and Internet hosting companies that account for a large percentage of the malware sites. This report provides both a basis for comparing changes over time and insight for possible action to mitigate or thwart malware attacks," said Steve Crocker, President Edgemoor Research Institute, Internet pioneer and inductee to the Internet Hall of Fame.
Malware attackers have also made effective use of cloud services, including file-sharing services, code repositories, and storage services. Dave Piscitello, Interisle partner, explains, "Most uses of anonymous file-sharing and code repositories are well-intentioned; however, malware attackers use these services to distribute source code, attack code, and files containing compromised credentials or cryptographic keys."
Cooperative efforts can mitigate malware attacks. Service providers, law enforcement officials, and government agencies must work together to combat cybercriminals. To learn more about the worst malware offenders, the most pressing malware concerns, and what measures are needed to reduce and eliminate malware distribution and growth, please visit https://interisle.net/MalwareLandscape2022.html.
About Interisle
Interisle's principal consultants are experienced practitioners with extensive track records in industry and academia and world-class expertise in business and technology strategy, Internet technologies and governance, financial industry applications, and software design. Every Interisle client benefits from the direct hands-on management of this core team, augmented by the specialized expertise of an extensive network of associates—a coherent, team approach with the low overhead of a lean, virtual organization.
About the Cybercrime Information Center
The Cybercrime Information Center is a repository for studies, measurements, data sets, statistics, and analyses of global security threats involving the Internet's Domain Name System (DNS), and numbering systems (Internet protocol, IP, and Autonomous System numbering, AS). The project operates through support or data contributed from Anti-Phishing Working Group (APWG), the Coalition Against Unsolicited Commercial Email (CAUCE), Domain Tools, InvaluementURI, Malware Patrol, MalwareURL, OpenPhish, PhishTank, The Spamhaus Project and The URLhaus Malware URL Exchange.
Contact Information
Dave Piscitello
dave@interisle.net
Source: Interisle